client
Task Sequence can't find a dependency that doesn't exit
 When I see 'Failed to run Task Sequence - This task sequence cannot be run because the program files for XXXXXXX cannot be locataed on a distribution point'
When I see 'Failed to run Task Sequence - This task sequence cannot be run because the program files for XXXXXXX cannot be locataed on a distribution point'
I go to Monitoring \ Distribution Status \ Content Status. It's the quickest way to search all package objects. Today the search came up with no results.
I exported the task sequence to make sense of it, found the ID in a section about OSDSubTaskSequenceTsReferencePackages -
<variable name="OSDSubTasksequenceTsReferenceApplications" property="TsReferenceApplications"></variable>
<variable name="OSDSubTasksequenceTsReferencePackages" property="TsReferencePackages">ZZZ00019,ZZZ0001F,ZZZ00020,ZZZ00024</variable></defaultVarList></subtasksequence>
What happened was someone removed a driver package and deleted it. The main task sequence still referenced it. To fix I modified the main task sequence, so it kicked off new policies.
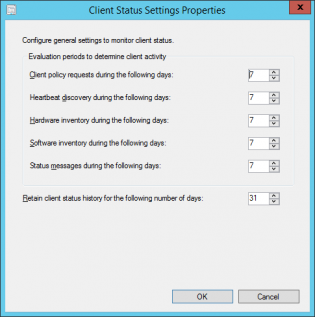
Setting the Client Status Settings for Client Activity based on AD logon
SCCM will mark a computer inactive if none of the activity checks happen
- Client policy request
- Heartbeat discovery
- Hardware Inventory
- Software Inventory
- Status messages sent
See technet
The default settings are 7 days for each of these settings which can be fine for a lot of businesses. If there are many devices that don't often connect to the network if may look as if there is more client health issues than there really is. To get an idea of how many devices have been on the network within x amount of days you can run the following query in the SQL Management Studio:
|
1 2 3 4 5 |
select sys.Name0, ClientActiveStatus, ClientState, ClientStateDescription, LastOnline from v_CH_ClientSummary cli join v_R_System sys on sys.ResourceID=cli.ResourceID where DATEDIFF(d, LastOnline, GetDate()) < 7 order by LastOnline desc |
This uses LastOnline (Connected to AD) to get a list of the last 7 days. Then all you need to do is modify the 7 in the query to higher values to get a number that represents a higher percentage of your fleet contacting the AD. It could be 14 days, 30 days.
This will change depending on VPN usage, Direct Access. Once you enable the Cloud Management Gateway this setting will need to be tweaked again not using this data as clients will request policy from the internet.
To configure these settings:
-
In the Monitoring workspace, click Client Status, then, in the Home tab, in the Client Status group, click Client Status Settings.
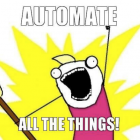
How To: Create Automatic Deployment Rules for Patch Tuesday Software Updates
Automatic deployment of updates is one of the best features of SCCM. Automation in general is awesome.
The best way to use Automatic deployment rules (ADR) is to have them run on Patch Tuesday which is the second Tuesday of the month when Microsoft releases their updates generally before 11:00 PST/PDT (I am Australian based so I set ADRs to run Wednesday Morning).
In this example I am deploying Windows 8.1 x64 critical, security and 'updates' updates.
1. Under the Software Library Node Software Updates click Automatic Deployment Rules then select 'Create Automatic Deployment Rule' from the Ribbon
2. In the Wizard name your ADR 'ADR: Windows 8.1 x64 Updates'
3. Click Browse and select your target collection
4. Change the Option to 'Create a new Software Update Group'. The other Option should really be called 'Wipe previous updates from Software Update Group' as that's what it does.
5. Click Next.
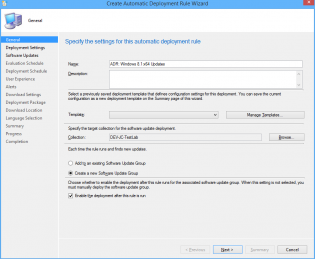
6. Ensure 'Automatically deploy all software updates found by this rule, and approve any license agreements. Also optionally enable the Wake-on-LAN tickbox.
7. Click Next
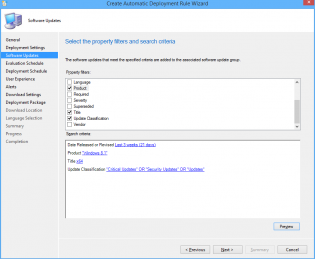
8. Choose Date Released or Revised, set it to Last 3 weeks.
9. Choose Product, set it to 'Windows 8.1'
10. Choose Update Classification, set it to “Critical Updates” OR “Security Updates” OR
“Updates”
11. Choose Title, set it to 'x64'. This is to filter out x86 updates.
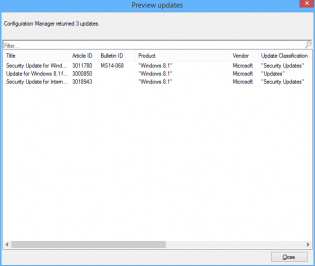
12. Click Preview, if you are doing this on Patch Tuesday you will see all the applicable updates that will be deployed. Otherwise you can change the date range for the example.
13. Click Next
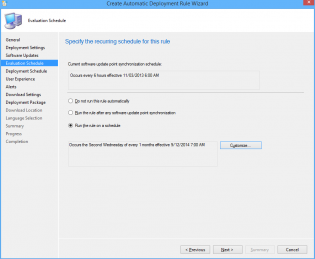
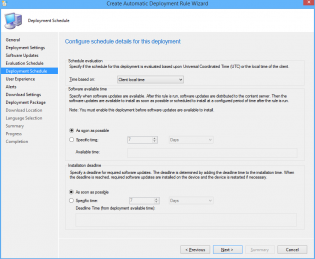
14. Choose 'Run the rule on a schedule.
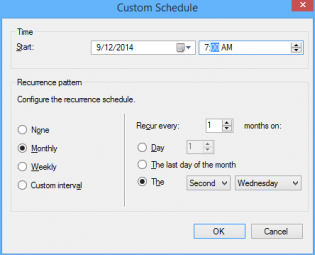
15. Click Customize and choose to run the rule every second Tuesday at the appropriate time depending what time zone you are in. Click OK (Not to important for the demo as you can run it manually)
16. Click Next
17. Customize the Deadline to 'As soon as possible'.
18. Click Next
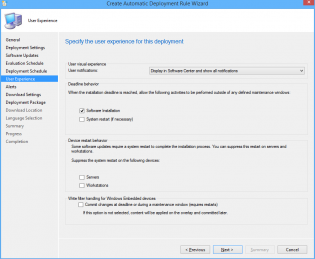
19. Change the User Experience to 'Display in Software Center and show all notifications'
20. Tick 'Software Installation'.
21. Click Next.
22. Click Next.
23. Click Next
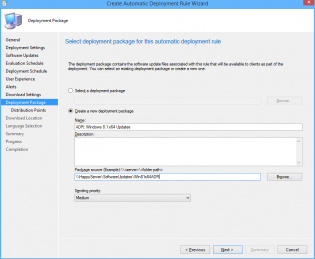
24. Choose Create a new deployment package.
25. Name it 'ADR: Windows 8.1 x64 Updates' and select a UNC share for storage of the software updates.
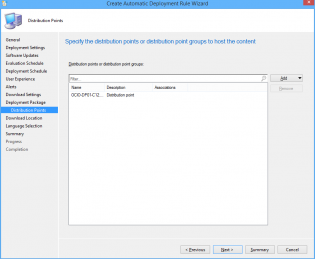
26. Add Distribution Points.
27. Click Next.
28. Click Next
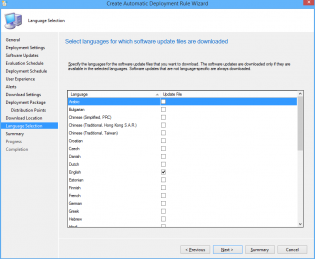
29. Select desired languages, click Next
30. Click Next, then Close.
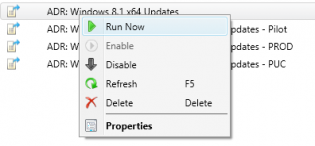
31. Right click on your newly created ADR and click 'Run Now'. You can monitor progress on the site server checking Program FilesMicrosoft Configuration ManagerLogsruleengine.log
32. Give it some time to download updates and distribute them then on the client machine run a machine policy update and verify updates install using Software Center
33. After having a play check out this post for some best practices to setting up all your Automatic Deployment Rules including Piloting your updates to a pilot group for 7 days.
34. Also check out this post to automate sending a report out on what updates are being deployed.
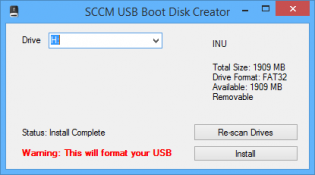
SCCM USB Boot disk creator
I made a little program that sets up usb drives to be bootable into OSD winpe. I made it because we are getting devices without dvd drives that can't pxe boot and our techs don't have access to create bootable usb's from the console as they need the dp cert and password.
You generate a boot iso from the console, then copy the cd contents to the source folder where the program resides.
Program and my bad source code (if anyone wants to improve it) https://send.estate/s?e=8d189f24f1c9ada[1]
Pre-Reqs:
Dot Net 3.5
A bootable iso generated from the SCCM Console
Instructions:
Copy all files from the bootable iso to the source folder that resides with the exe.
Distribute as you wish.
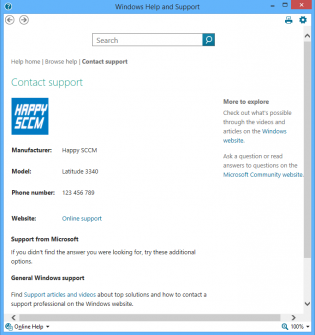
Set Computer Model OEM Information during task sequence.
Make your SOE a little bit fancy
To set the Computer Model information during OSD you just need to add a run command line step
Powershell.exe -ExecutionPolicy Bypass -Command $model = Get-WmiObject win32_computersystem model;Set-ItemProperty -Path HKLM:SoftwareMicrosoftWindowsCurrentVersionOEMInformation -Name Model -Value $model.model
Other Settings you can put in HKLMSoftwareMicrosoftWindowsCurrentVersionOEMInformation
Logo - Pathtologo.bmp
Manufacturer
SupportPhone
SupportURL
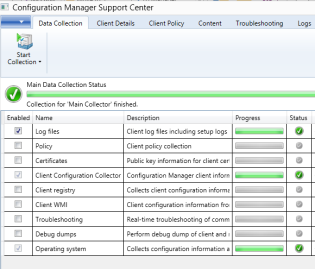
Microsoft Configuration Manager Support Center
Have you ever needed someone to collect logs off a machine and came to find that the vital log you wanted wasn't collected? Lost in the sea of logs?
Microsoft feels your pain!
Microsoft has released an excellent support tool to assist in troubleshooting ConfigMgr. It can collect logs, policys, wmi, registry etc; from remote or local machines. Also includes a log viewer that groups logs by function. I think it will eventually replace CMTrace.
It's in BETA so read the release notes! Update: It's released!
http://www.microsoft.com/en-us/download/details.aspx?id=42645