Posts
Slow Software Center search results
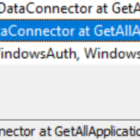
Currently Software Center will use WMI to query all available software for the computer, then it will ask the management point for user assigned apps.
If your computer is a bit slow/old the wait time checking WMI can be painful. You can check this on the client log SCNotify_MONASH@%username%_1.log
Please vote for my Uservoice - https://configurationmanager.uservoice.com/forums/300492-ideas/suggestions/39082435-speed-up-software-centre-searches-by-returning-use
If your SQL is slow you have another problem.. You can check this on the MP UserService.log - Search for GetFilteredApplications.
SQL Fixes:
Set the right compatibility level - https://support.microsoft.com/en-au/help/3196320/sql-query-times-out-or-console-slow-on-certain-configuration-manager-d
Reindex right - https://www.scconfigmgr.com/2017/01/03/configuration-manager-sql-database-maintenance/
Task Sequence can't find a dependency that doesn't exit
 When I see 'Failed to run Task Sequence - This task sequence cannot be run because the program files for XXXXXXX cannot be locataed on a distribution point'
When I see 'Failed to run Task Sequence - This task sequence cannot be run because the program files for XXXXXXX cannot be locataed on a distribution point'
I go to Monitoring \ Distribution Status \ Content Status. It's the quickest way to search all package objects. Today the search came up with no results.
I exported the task sequence to make sense of it, found the ID in a section about OSDSubTaskSequenceTsReferencePackages -
<variable name="OSDSubTasksequenceTsReferenceApplications" property="TsReferenceApplications"></variable>
<variable name="OSDSubTasksequenceTsReferencePackages" property="TsReferencePackages">ZZZ00019,ZZZ0001F,ZZZ00020,ZZZ00024</variable></defaultVarList></subtasksequence>
What happened was someone removed a driver package and deleted it. The main task sequence still referenced it. To fix I modified the main task sequence, so it kicked off new policies.
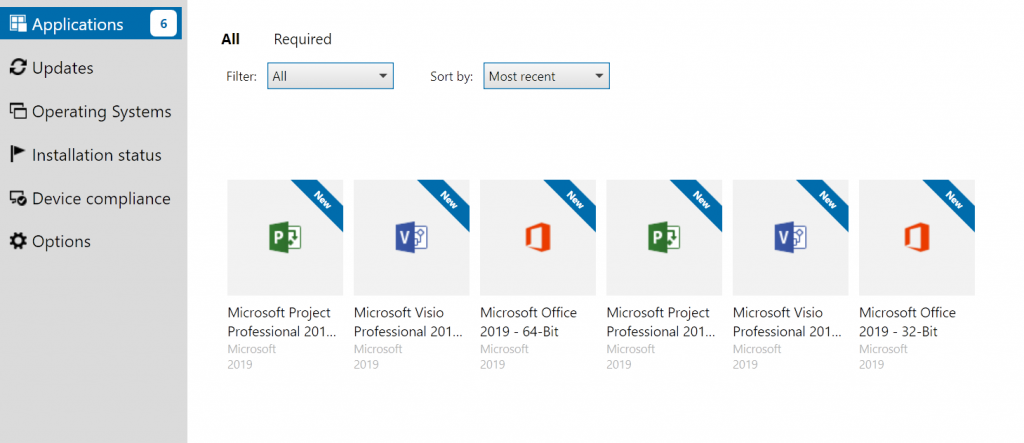
Deploying Office 2019 VL
Office 2019 now uses click-to-run technology instead of 'setup /admin' there are a few changes, probably for the best in the long run.
Create Config Files
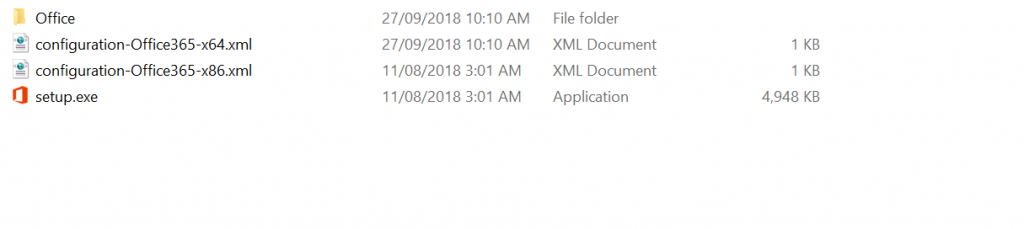
First you need to download to Office Deployment tool
This is a self extracting file that spits out setup.exe and 2 sample config files - one for 32-bit and one for 64-bit.
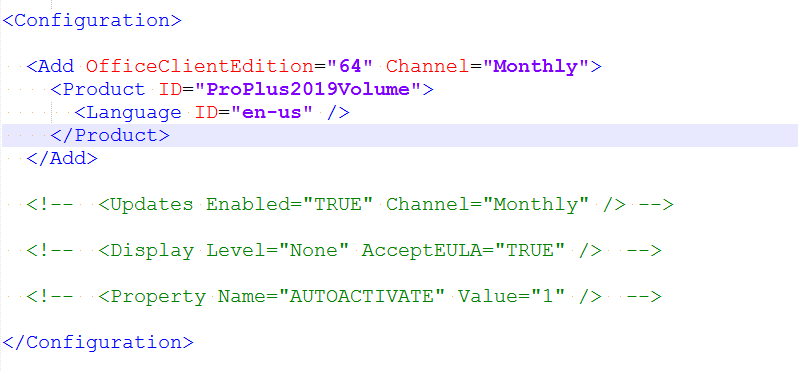
Edit the edition you want to download. If you want the Volume License version change the Product ID to 'ProPlus2019Volume'
You don't need to add Visio or Project as they are also downloaded.
Save the file and run 'setup.exe /download configuration-Office365-x64.xml'.
This will run in the background and download into a subfolder - Office.
Now you have the files you can make configurations using these resources
https://config.office.com/ - Spits out config files for Office 365 - At time of writing it isn't made for 2019 yet but should work ok.
https://docs.microsoft.com/en-gb/DeployOffice/office2019/deploy - Documentation on customising the confiuration files.
If you want a head start I've made config files for Office, Project and Visio - Download
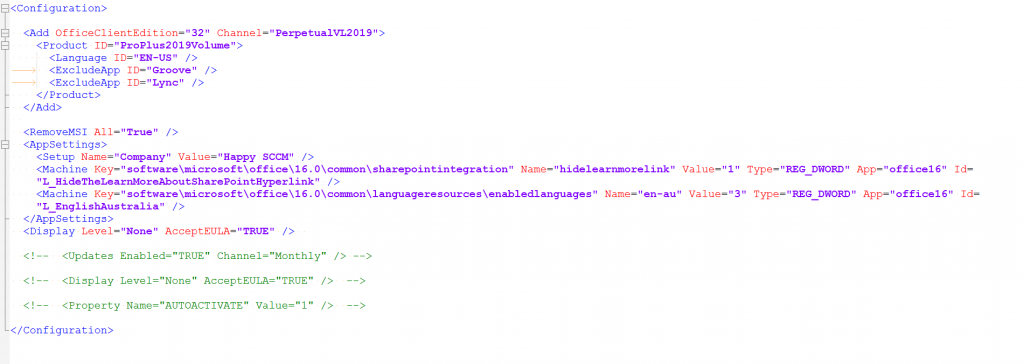
Example - Office 32-Bit, exclude OneDrive and Skype, accept EULA, Silent install, some customisations from Config.office.com
Test
To test your config files run setup.exe with the configure switch
setup.exe /configure configuration-OfficeProPlus-x86.xml
Deploy
Create an application in SCCM - with your files.
Deployment type - Script Installer
For Detection Methods:
Office - 32-Bit: %ProgramFiles(x86)%\Microsoft Office\root\Office16\Winword.exe
Office - 64-Bit: %ProgramFiles%\Microsoft Office\root\Office16\WINWORD.EXE
Project - 32-Bit: %programfiles(x86)%\Microsoft Office\root\Office16\WINPROJ.EXE
Project - 64-Bit: %ProgramFiles%\Microsoft Office\root\Office16\WINPROJ.EXE
Visio - - 32-Bit: %programfiles(x86)%\Microsoft Office\root\Office16\VISIO.EXE
Project - 64-Bit: %ProgramFiles%\Microsoft Office\root\Office16\VISIO.EXE
KMS
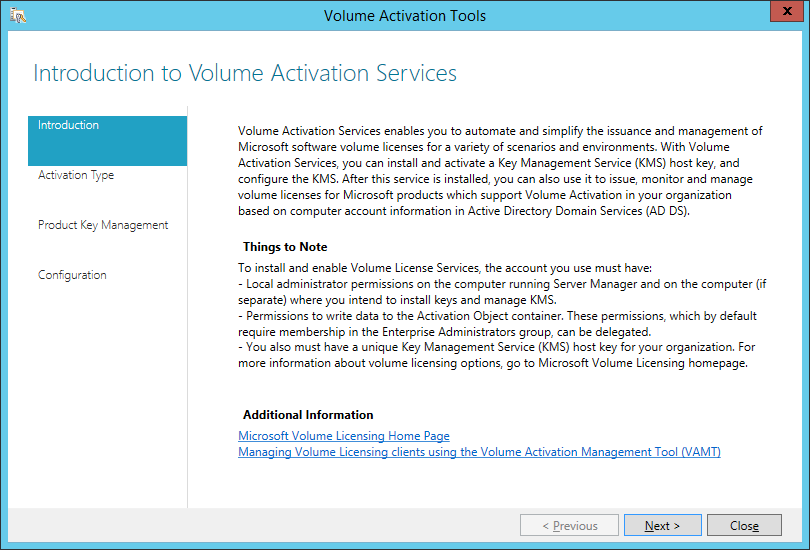
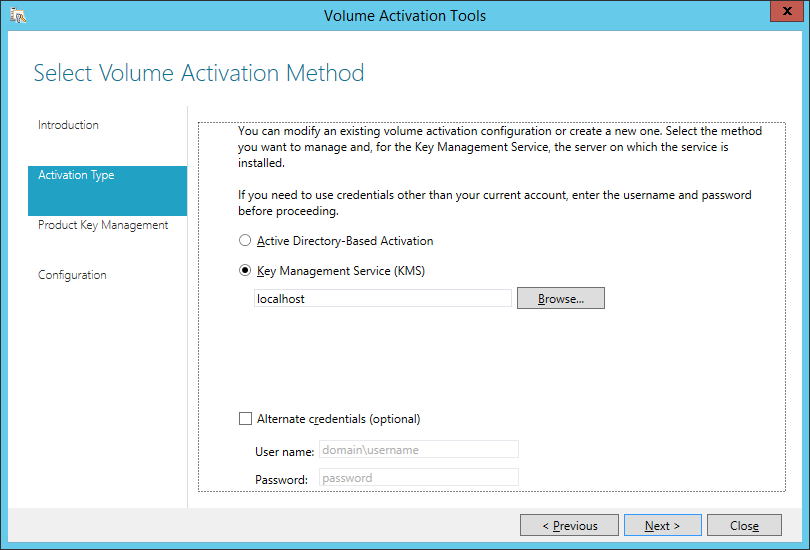
Download the Volume license app http://www.microsoft.com/downloads/details.aspx?FamilyID=878fef7e-3f4d-4d22-a423-f447c0f5bfdd
On the KMS server run the exe.
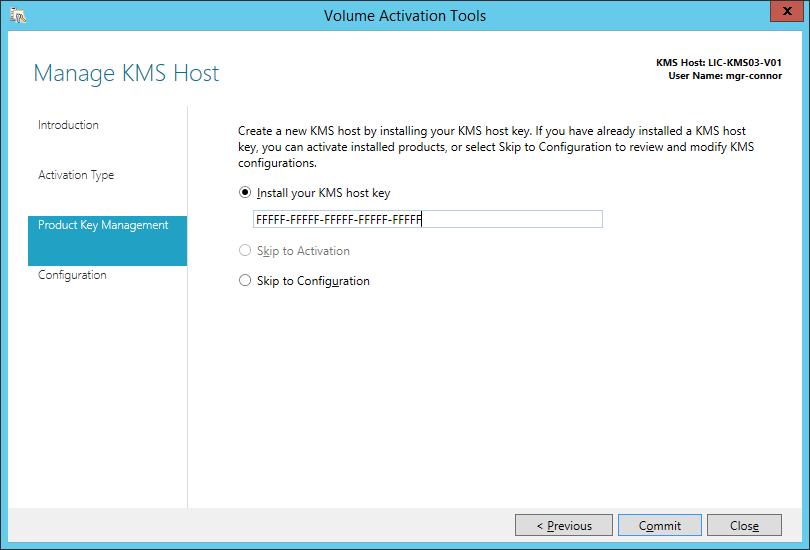
Get your Office 2019 KMS Key from your Key Holder
Don't Click Commit! Click Cancel as you already have this configured
Disable the OneDrive Notification/Advertisement
This will popup for each user on first login. There is a registry entry that you can use to trick OneDrive to thinking it has already done this.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive
Name: ClientNotSignedInBalloonState
Type: REG_DWORD
Data: 2
To put this in your default profile during OSD:
reg load HKU\DefaultTemp "C:\Users\Default\NTUSER.DAT"
reg add "HKU\DefaultTemp\Software\Microsoft\OneDrive" /v ClientNotSignedInBalloonState /t REG_DWORD /d 2 /F
reg unload HKU\DefaultTemp
Edge browser crashes on load - Windows 1703
Update from Microsoft:
Fixed in updates -
- 1709 - https://support.microsoft.com/en-us/help/4093105/windows-10-update-kb4093105 | https://www.catalog.update.microsoft.com/Search.aspx?q=kb4093105
- 1703 - https://support.microsoft.com/en-us/help/4093117/windows-10-update-kb4093117 | https://www.catalog.update.microsoft.com/Search.aspx?q=KB4093117
We have seen roaming profiles in Windows 10 1703 unable to use the Edge browser if the profile was originally first created with Windows 10 1607.
The address bar briefly displays ms-appx-web:///assets/errorpages/acr_error.htm#https://go.microsoft.com/fwlink/?LinkId=525773 then closes.
In our scenario, enabling the group policy ‘Prevent the First Run webpage from Opening on Microsoft Edge’ fixes the issue so it seems that the 1607 profile has an issue with first run.
Another fix (found in forums) is an undocumented one that does resolve crashes as well is
|
1 |
reg add "HKCU\Software\Microsoft\Internet Explorer\Spartan" /v RAC_LaunchFlags /t REG_DWORD /d 1 /f |
however I don't recommend it as we don't know what it will affect. Maybe use it as a workaround temporarily.
SCCM client = None after deploying an operating system
In an environment where you use certificates this can happen.
CLientIDManagerStartup.log will mention
Regtask: Failed to refresh MP. Error: 0x80004005
alot of times...
Below I have the 2 fixes!
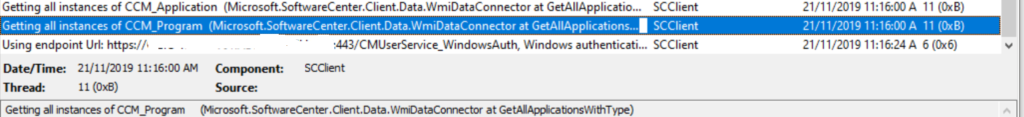
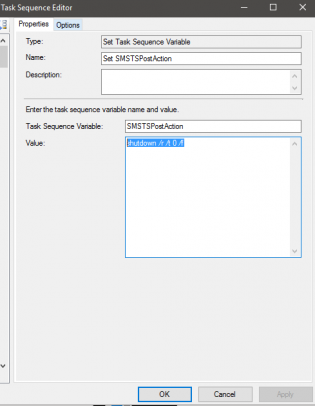
Fix 1 is to take advantage of the TS Variable SMSTSPostAction to restart the computer once completed
with the value 'shutdown /r /t 0 /f'
This should ensure the cert is requested.
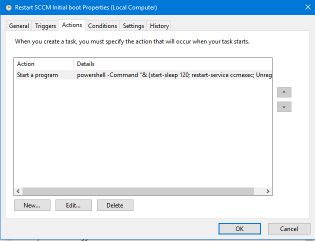
Fix 2:
From testing - after Fix 1 you may need to re-start the SCCM agent.
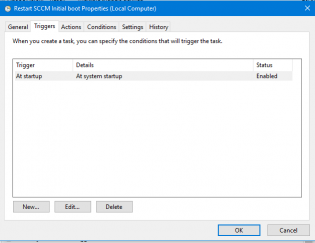
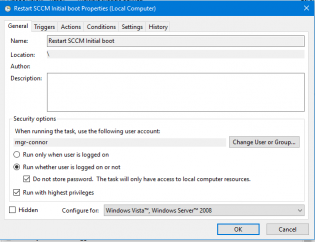
To do this create a scheduled task that runs on start-up
Program: Powershell
Arguments: -Command "& {start-sleep 120; restart-service ccmexec; Unregister-ScheduledTask -TaskName 'Restart SCCM Initial boot' -Confirm:$false;}"
Run whether or not user is logged on.
Export the scheduled task as 'RestartSCCM.xml' and create a package and command line to run at the end of OSD
SCHTASKS.exe /CREATE /RU system /XML "RestartSCCM.xml" /TN "Restart SCCM Initial boot"
Happy deploying!
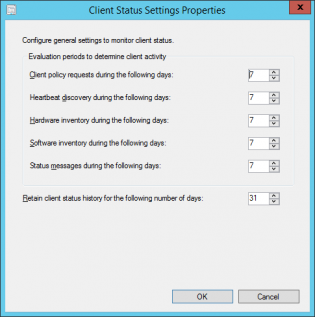
Setting the Client Status Settings for Client Activity based on AD logon
SCCM will mark a computer inactive if none of the activity checks happen
- Client policy request
- Heartbeat discovery
- Hardware Inventory
- Software Inventory
- Status messages sent
See technet
The default settings are 7 days for each of these settings which can be fine for a lot of businesses. If there are many devices that don't often connect to the network if may look as if there is more client health issues than there really is. To get an idea of how many devices have been on the network within x amount of days you can run the following query in the SQL Management Studio:
|
1 2 3 4 5 |
select sys.Name0, ClientActiveStatus, ClientState, ClientStateDescription, LastOnline from v_CH_ClientSummary cli join v_R_System sys on sys.ResourceID=cli.ResourceID where DATEDIFF(d, LastOnline, GetDate()) < 7 order by LastOnline desc |
This uses LastOnline (Connected to AD) to get a list of the last 7 days. Then all you need to do is modify the 7 in the query to higher values to get a number that represents a higher percentage of your fleet contacting the AD. It could be 14 days, 30 days.
This will change depending on VPN usage, Direct Access. Once you enable the Cloud Management Gateway this setting will need to be tweaked again not using this data as clients will request policy from the internet.
To configure these settings:
-
In the Monitoring workspace, click Client Status, then, in the Home tab, in the Client Status group, click Client Status Settings.
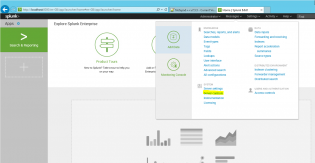
Monitoring your fleets event logs - Part 2
Install Splunk - It's free! https://www.splunk.com/en_us/download/splunk-enterprise.html
Modify Program Files\Splunk\etc\system\local\inputs.conf
Add the lines
[WinEventLog]
evt_resolve_ad_obj = 1
Then we need to reboot splunk, in Splunk click Settings, then Server controls and click Restart Splunk
Next we need to add our data source, click Add Data from the launch screen, then monitor
Choose Local Events then ForwardedEvents and click Next

Click Create a new index, call it ForwardedEvents, click Save, change the Index to ForwardedEvents and then click Review, Submit
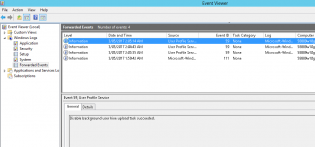
Give it some time to collect a few logins, then go to Search & Reporting
index="forwardedevents" LogName="Microsoft-Windows-User Profile Service/Operational" (EventCode=1 OR EventCode=2 OR EventCode=6 OR EventCode=7) | transaction ComputerName startswith=eval(EventCode=1) endswith=eval(EventCode=2) | table ComputerName, duration
So I'm using the selected data, filtering for 4 event codes, then getting the time between event code 1 and 2, and putting it into a table..
Edit: This search can be a bit funny, the delay ended up being between synching the roaming profile so I've also ran
index="forwardedevents" LogName="Microsoft-Windows-User Profile Service/Operational" (EventCode=1 OR EventCode=2 OR EventCode=6 OR EventCode=7) | transaction ComputerName startswith=eval(EventCode=6) endswith=eval(EventCode=7) | table ComputerName, duration
Then click on the Visualization tab
This also lets you dive into each login by clicking one and get the event logs!
You can save this as a report, dashboard and share with people.
There is so much more you can do with this software, and it takes some time to learn it. Will post more as I do..
Monitoring your fleets event logs - Part 1
Windows has an amazing feature that let's you collect logs from remote computers, it's called Windows Event forwarding and is pretty easy to set up. Once we have this data we can use free tools such as Splunk or GrayLog to analyse the data, find patterns, fix.
Below is the way to get started collecting the user profile logs to analyse things such as login performance with roaming profiles, something we are dealing with right now! Please note you need to enable winrm on your computers for forwarding to work.
First you need a machine that will be the data collectior.
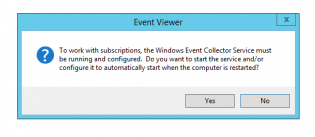
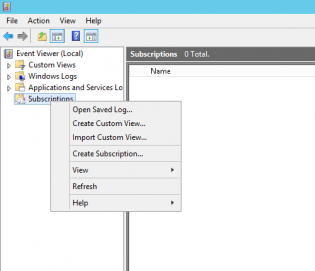
- On that machine open Event Viewer and right click Subscriptions. You may get the following message to enable the service on startup
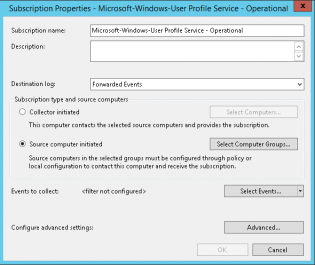
2. Now you should only collect data that you will use, in this example we are collecting the Microsoft-Windows-User Profile Service/Operational events so we will call it Microsoft-Windows-User Profile Service - Operational
3. Change the type to Source computer initiated and click Select Computer Groups
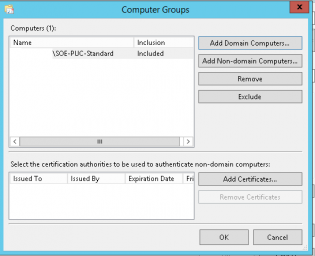
4. Add the group of machines to the Computer list and click OK
5. Click Select Events
6. We now select the Applications and Services Logs\Microsoft\Windows\User Profile Service
7. You can configure advanced settings to control how the computers forward the events.
8. Click OK
9. To get clean data we need to change the format of returned events by running the command:
wecutil ss "Microsoft-Windows-User Profile Service - Operational" /cf:Events
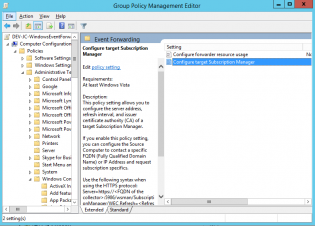
10. Next you deploy a group policy that tells your computers to go to the data collector for jobs
Create a group policy using Computer Configuration\Policies\Administrative Templates\Windows Components\Event Forwarding
11. Select Configure target Subscription Manager
12. Set to Enabled
13. Click Show
14. Insert the line
Server=http://SERVER.FQDN:5985/wsman/SubscriptionManager/WEC,Refresh=60
15. Replace SERVER.FQDN with your data collector's name.
16. To test run GPUPDATE /FORCE on the remote machine
17. If successful, on the data machine you will see the number of source computers change and logs in the forwarded events
Visit https://blogs.technet.microsoft.com/jepayne/2015/11/23/monitoring-what-matters-windows-event-forwarding-for-everyone-even-if-you-already-have-a-siem/ for more information.
PART 2