September, 2014
Modular Task Sequence groups - Just an idea
Maik Koster has created a really good tool that monitors/ keeps backup of task sequence changes
expanding from this it may be possible to mark groups of your task sequences as modules. So say when a task sequence changes the script would then record the xml changes of that module group and replace in all task sequences where it is used. It would be perfect for the apply driver steps.
I haven't really worked it all out as I don't have many task sequences for it to be super useful and it would be a bit to hacky. I hope Microsoft can implement modules and version control in the next release of ConfigMgr.
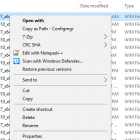
Add a Right Click Copy Folder or File path menu option in Windows Explorer
SCCM ConfigMgr doesn't like quotes around paths when adding packages or Wims, etc so the secret shh shift + right click copy as path isn't that handy.
Here's a reg file to add a special right click option for ConfigMgr
KB2918614 - UAC GATE
Update 13/11:
A new hotfix was released:
http://support.microsoft.com/kb/3008627
After install above hotfix, you can use below registry key manually as a switch to enable or disable the UAC :
Under Key “HKLMSOFTWAREPoliciesMicrosoftWindowsInstaller”, create a DWORD: “NoUACforHashMissing” and set its Value to 1.
Update 17/09:
You can whitelist existing msi's. Not tested yet, will test and deploy as a dependency for the update.
https://send.estate/s?e=8d19fef3f12531a
After further discussion with our product team. They provided us a new workaround that you can add the existing applications into a whitelist. Here is the details:
Whitelisting: If you trust the application that it is always digitally signed and does not contain any malicious payload, add it to the whitelist.
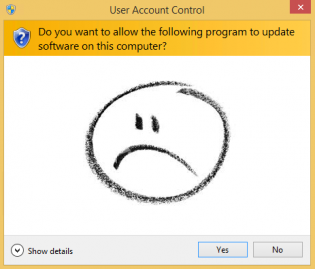
There are two REG keys needed for whitelisting:
1) Need Whitelisting: Under Key “HKLMSOFTWAREPoliciesMicrosoftWindowsInstaller”, create a DWORD: “SecureRepairPolicy” and set its Value to 2.
We (Microsoft) wrote a script to add the white list for customer automatically. Please download the attachment from https://send.estate/s?e=8d19fef3f12531a and rename it as .vbs. Double clicking it will help to add the whitelist for all of the installed MSI application.
Update on KB2918614.
Microsoft:
This security update resolves a privately disclosed vulnerability in Microsoft Windows. The vulnerability could allow elevation of privilege if an attacker runs a specially crafted application that attempts to repair a previously-installed application. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability.
Workaround if you have problems with repairing application:
==================================================
1. Uninstall the application and reinstall it with the security update installed. (sourcehash file generated with security update)2. Manually copy the sourcehash file to c:windowsinstaller folder. As the sourcehash file is generated based on the application files, the sourcehash file generated on computer A can be used on computer B.
Another Workaround:
Not sure of the consequences fully yet - Remove
HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionInstallerUserDataS-1-5-18Products{guid}InstallPropertiesLocalPackage
This then uses Windows Installer Source list for msi repair without promtping. And generates you a fresh sourcehash.
Uninstall Commands (via SCCM Package):
Windows 7 x64 Uninstall: c:windowssysnativecmd.exe /c dism.exe /online /remove-package /PackageName:"Package_for_KB2918614~31bf3856ad364e35~amd64~~6.1.1.4" /quiet /norestart
Windows 8 x64 Uninstall: c:windowssysnativecmd.exe /c dism.exe /online /remove-package /PackageName:"Package_for_KB2918614~31bf3856ad364e35~amd64~~6.3.1.4" /quiet /norestart
Windows 2008 R2 x64 Uninstall: c:windowssysnativecmd.exe /c dism.exe /online /remove-package /PackageName:"Package_for_KB2918614~31bf3856ad364e35~amd64~~6.1.1.4" /quiet /norestart
Sysnative is required otherwise you get error 11.
Windows 7 x86 Uninstall: cmd.exe /c dism.exe /online /remove-package /PackageName:"Package_for_KB2918614~31bf3856ad364e35~x86~~6.1.1.4" /quiet /norestart
The work arounds aren't that easy when you have over a 1000 apps, the update would be ok in your base image.
Thanks to Jörgen Nilsson for discovering this via http://ccmexec.com/2014/09/kb2918614-windows-installer-triggers-uac/
Take advantage of OEM Settings to display OSD state!
I have 2 scenarios that allows techs to determine the computers state. When the task sequence fails or when a Lab computer hasn't been added to a lab group. It's easy to enable the oembackground and rename a jpg picture. Group policy reg can disable the background picture.
For the first scenario you enable 'Continue on Error' for the very first group and have a catcher group at the end of the task sequence that runs only if TSVariable '_SMSTSLastActionSucceeded' = False. MDT Task sequences are setup like this by default. It is best if the captured wim you are deploying already has the background file in it for scenarios where it fails due to not having any network access.
In the catcher group you will need 3 steps:
1. Copy jpg: Run command line with disable 64-bit file system redirection using a package with the jpg file (Not needed if jpg is in the captured wim):
cmd.exe /c xcopy Fail-Wallpaper.jpg C:\Windows\System32\oobe\info\Backgrounds /i /y
2. Rename jpg: Run command line with disable 64-bit file system redirection
cmd /c ren C:\Windows\System32\oobe\info\Backgrounds\Fail-WallpaperMU1.jpg backgroundDefault.jpg
3. Enable OEMWallpaper: Run command line with disable 64-bit file system redirection
cmd /c reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\Background /v OEMBackground /t REG_DWORD /d 1 /f /reg:64
I can expand and provide scripts on how I determine whether the computer is part of a lab ou/group based on name and ad object. Let me know!
Edit: This entry is for Windows 7, In Windows 8.1 you should do similiar but use the lockscreen - See the post on Windows 8.1 setting lockscreen and wallpaper for more information